-
Implementing RecyclerView in Android with Kotlin
Learn how to use RecyclerView to efficiently display large lists of data in your Android apps using Kotlin programming language.
-

Implementing Toast Messages in Android Using Kotlin
Learn how to implement toast messages in Android using Kotlin with a practical example. Enhance your app’s user experience.
-
How to Create Material Alert Dialog in Android with Kotlin
Learn to build Material 3 Alert Dialog in Android using Kotlin with step-by-step instructions and examples.
-

Trees in Data Structures Including Binary Trees and AVL Trees
Learn about the different types of trees in data structures, including binary trees, AVL trees, B-trees, and Trie trees, and their properties.
-
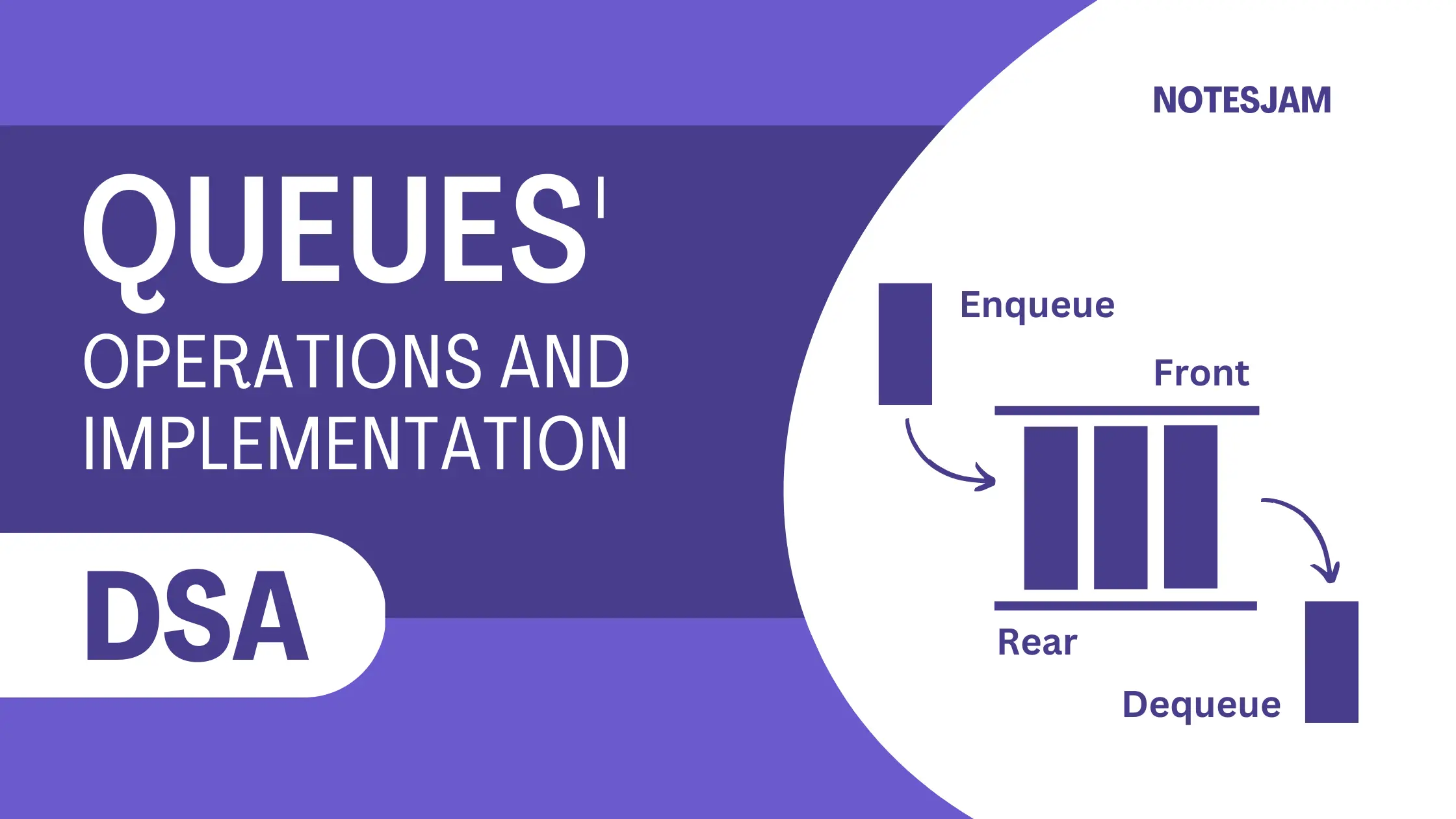
Queues in Data Structures: Operations, Implementation, and Applications
Learn about queue implementation using arrays and linked lists, explore operations with examples and discover their applications in data structures.